AppTrana
Getting Started
Frequently Asked Questions
Product Details
Browser Protection
API Scan Coverage for OWASP Top 10
Malware Scanning for File Uploads
Whitelist Vulnerabilities on the AppTrana WAAP
API Request to Purge CDN Data
Analysis page - Attack Trend Visualisation
Update Origin Server Address
Advanced Behavioral DDoS
BOT Protection
Asset Discovery
Customize Application Behavior with Bot Score
Restricted Admin User
OWASP API Security Top 10 2023 – AppTrana API Protection
Self Service Rules
ASN based IP Whitelisting
Enhance Your API Security with API Classification
SwyftComply for API Scan
Custom Bot Configuration
Configure Custom Error Pages in AppTrana
Configuring Custom Error Page in AppTrana
Enabling SIEM Integration
API Discovery Feature
SwyftComply
Analysis page - Access Trend Visualization
Manage WAAP Email Alerts
Configuring Custom Error and Maintenance Pages in AppTrana WAAP
Enable and Configure Single Sign-On
Origin Health Check Mechanism
WAF Automated Bypass and Unbypass
False Positive Analysis Report on WAAP
DNS Management
Product User Guide
Indusface WAS
Getting Started
Product User Guide
Summary
Dashboard
Malware Monitoring[MM]
Vulnerability Assessment[VA]
Application Audit[AA]
Reports
Settings
Asset Monitoring
New Reporting Structure
API Security Audit
Frequently Asked Questions
Feature Summary
AcuRisQ – Risk Management with Advanced Risk Scoring
Automated API Scanning
WAS Consulting License
API Key Based - Scan Log Export
WAS Defacement Checks
SIEM Integration with Sumo Logic
Indusface WAS Scanned Vulnerabilities
Indusface Newsletter
Indusface Product Newsletter - October 2021
Indusface Product Newsletter- April 2021
Indusface Product Newsletter-January21
Indusface Product Newsletter - June 20
Indusface Product Newsletter - October 19
Indusface Product Newsletter - August 19
Product Newsletter of May 19
Product Newsletter of March 19
Product Newsletter of January 19
WAF Portal Revamp June 18
Product Newsletter of July 18
Product Newsletter of May 18
Product Newsletter of March 18
Product Newsletter of February 18
Product Newsletter of January 18
Indusface Product Newsletter - March 2022
Indusface Product Newsletter - February 2023
Indusface Product Newsletter- October 2022
Zero Day Vulnerability Reports
Vulnerabilities Detected in 2016
CRS vs. Zero Day Vulnerability - December 2016
CRS vs. Zero Day Vulnerability - November 2016
CRS vs. Zero Day Vulnerability - October 2016
CRS vs Zero Day Vulnerability - September 2016
CRS Vs Zero Day Vulnerabilities - August 2016
Vulnerabilities Detected in 2017
Vulnerability Report of April 17
Vulnerability report for Apr 3rd - Apr 9th 17
Vulnerability report for April 17th - Apr 23rd 17
Vulnerability report of April 10th - April 16th
Vulnerability Report of March 17
Vulnerability report for Mar 20th - Mar 26th
Vulnerability report for Mar 13th - Mar 19th
Vulnerability report for 27th Feb - 5th Mar
Vulnerability report for Mar 27th - Apr 2nd
Vulnerability report for Mar 6th - Mar 12th
Vulnerability Report of February 17
Vulnerability Report of January 17
Vulnerability Report of December 17
Vulnerability Report of November 17
Vulnerability Report of August 17
Vulnerability Report of September 17
Vulnerability Report of October 17
Vulnerability Report of July 17
Vulnerability Report of June 17
Vulnerability Report of May 17
Vulnerabilities Detected in 2018
Vulnerability Report of December 18
Vulnerability Report of November 18
Vulnerability Report of October 18
Vulnerability Report of September 18
Vulnerability Report of August 18
Vulnerability Report of July 18
Vulnerability Report of June 18
Vulnerability Reports of May 18
Vulnerability Report of April 18
Vulnerability Report of March 18
Vulnerability Report of February 18
Vulnerability Report of January 18
Vulnerabilities Detected in 2019
Vulnerability Report of December 19
Vulnerability Report of November 19
Vulnerability Report of October 19
Vulnerability Report of September 19
Vulnerability Report of August 19
Vulnerability Report of July 19
Vulnerability Report of June 19
Vulnerability Report of May 19
Vulnerability Report of April 19
Vulnerability Report of March 19
Vulnerability Report of February 19
Vulnerability Report of January 19
vulnerabilities Detected in 2020
Vulnerability Report of December 20
Vulnerability Report of November 20
Vulnerability Report of October 20
Vulnerability Report of Sep 20
Vulnerability Report of July 20
Vulnerability Report of June 20
Vulnerability Report of May 20
Vulnerability Report of April 20
Vulnerability Report of March 20
Vulnerability Report of February 20
Vulnerability Report of January 20
Vulnerabilities Detected in 2021
Vulnerability Report of November 21
Vulnerability Report of October 21
Vulnerability Report of September 21
Vulnerability Report of August 21
Vulnerability Report of July 21
Vulnerability Report of June 21
Vulnerability Report of May 21
Vulnerability Report of April 21
Vulnerability Report of March 21
Vulnerability Report of February 21
Vulnerability Report of January 21
Vulnerability Report of December 21
Vulnerabilities Detected in 2022
Vulnerability Report of January 22
Vulnerability Report of February 22
Vulnerability Report of March 22
Vulnerability Report of April 22
Vulnerability Report of May 22
Vulnerability Report of June 22
Vulnerability Report of July 22
Vulnerability Report of August 22
Vulnerability Report of September 22
Vulnerability Report of October 22
Vulnerability Report of November 22
Zero-Day Vulnerability Report - December 2022
Vulnerabilities Detected in 2023
Vulnerability Report of May 23
Vulnerability Report of March 23
Vulnerability Report of August 23
Vulnerability Report of July 23
Vulnerability Report of April 23
Vulnerability Report of November 23
Vulnerability Report of June 23
Vulnerability Report of December 23
Vulnerability Report of February 23
Vulnerability Report of January 23
Vulnerability Report of September 23
Vulnerability Report of October 23
Vulnerabilities Detected in 2024
Vulnerability Report of October 2024
Vulnerability Report of April 2024
Vulnerability Report of July 2024
Vulnerability Report of May 2024
Vulnerability Report of September 2024
Vulnerability Report of February 2024
Vulnerability Report of December 2024
Vulnerability Report of January 2024
Vulnerability Report of June 2024
Vulnerability Report of March 2024
Vulnerability Report of November 2024
Vulnerability Report of August 2024
Security Bulletin
Vulnerabilities 2024
Hotjar's OAuth+XSS Flaw Exposes Millions at Risk of Account Takeover
Critical Apache OFBiz Zero-day AuthBiz (CVE-2023-49070 and CVE-2023-51467)
CVE-2024-4879 & CVE-2024-5217 Exposed - The Risks of RCE in ServiceNow
ScreenConnect Authentication Bypass (CVE-2024-1709 & CVE-2024-1708)
CVE-2024-4577 – A PHP CGI Argument Injection Vulnerability in Windows Servers
CVE-2024-8517 – Unauthenticated Remote Code Execution in SPIP
CVE-2024-1071 – Critical Vulnerability in Ultimate Member WordPress Plugin
Cryptocurrency Mining Attack Exploiting PHP Vulnerabilities: An Emerging Threat
Oracle WebLogic Server Deserialization
ApacheStructs_VG
Apache Struts 2 Vulnerability CVE-2023-50164 Exposed
Unpacking the Zimbra Cross-Site Scripting Vulnerability(CVE-2023-37580)
Adobe ColdFusion Vulnerabilities Exploited in the Wild
Remote Unauthenticated API Access Vulnerabilities in Ivanti
Multiple Moveit Transfer Vulnerabilities
HTTP/2 Rapid Reset Attack Vulnerability
CVE-2024-9264 - Grafana’s SQL Expressions Vulnerability
CVE-2024-8190 – OS Command Injection in Ivanti CSA
Apache log4j RCE vulnerability
Table of Contents
- Latest WAS Reporting Structure
- How are the vulnerability instances segregated/grouped?
- How is the vulnerability instances grouping is done?/How many levels of grouping is done and with what methodology?
- What does ‘Number of Places’ mean? What is the criteria?
- What does ‘types of vulnerability’ mean ?
- How is the severity of a vulnerability defined?
- How can I create a report?
- How to create a user?
- How can I change password?
- How to schedule a scan?
- My website is too big for one day scan, Is there an option to scan for more than 10 hours? How can I trigger it?
- What is Closure Report? How can I use it?
- All Categories
- Indusface WAS
- Frequently Asked Questions
- Reports and Settings
Reports and Settings
Updated
by Author
- Latest WAS Reporting Structure
- How are the vulnerability instances segregated/grouped?
- How is the vulnerability instances grouping is done?/How many levels of grouping is done and with what methodology?
- What does ‘Number of Places’ mean? What is the criteria?
- What does ‘types of vulnerability’ mean ?
- How is the severity of a vulnerability defined?
- How can I create a report?
- How to create a user?
- How can I change password?
- How to schedule a scan?
- My website is too big for one day scan, Is there an option to scan for more than 10 hours? How can I trigger it?
- What is Closure Report? How can I use it?
Latest WAS Reporting Structure
How are the vulnerability instances segregated/grouped?
Indusface follows a unique method of grouping of instances of vulnerabilities which would help users easily identify the quantum of risk that the application is exposed. For more details click here.
How is the vulnerability instances grouping is done?/How many levels of grouping is done and with what methodology?
Grouping is done in three levels. Listing of the vulnerability on the reports are by OWASP Top 10 category and under each category based on instances of vulnerabilities found, grouping is done with a specific methodology. Click here to view the complete explanation.
What does ‘Number of Places’ mean? What is the criteria?
It means, number of places a fix is actually required. For example, if vulnerability is found at config level, number of places will be one. If vulnerability is found in method, it will be number of methods it is found and so on.
What does ‘types of vulnerability’ mean ?
Types of vulnerability is the category of vulnerability found. For example, SQL Injection is a category. OS Command Injection is a category which can also be mentioned as vulnerability type.
How is the severity of a vulnerability defined?
Severity of vulnerability is determined by CVSS V3 Score of the vulnerability.
How can I create a report?
Click Create Report button in Reports page.
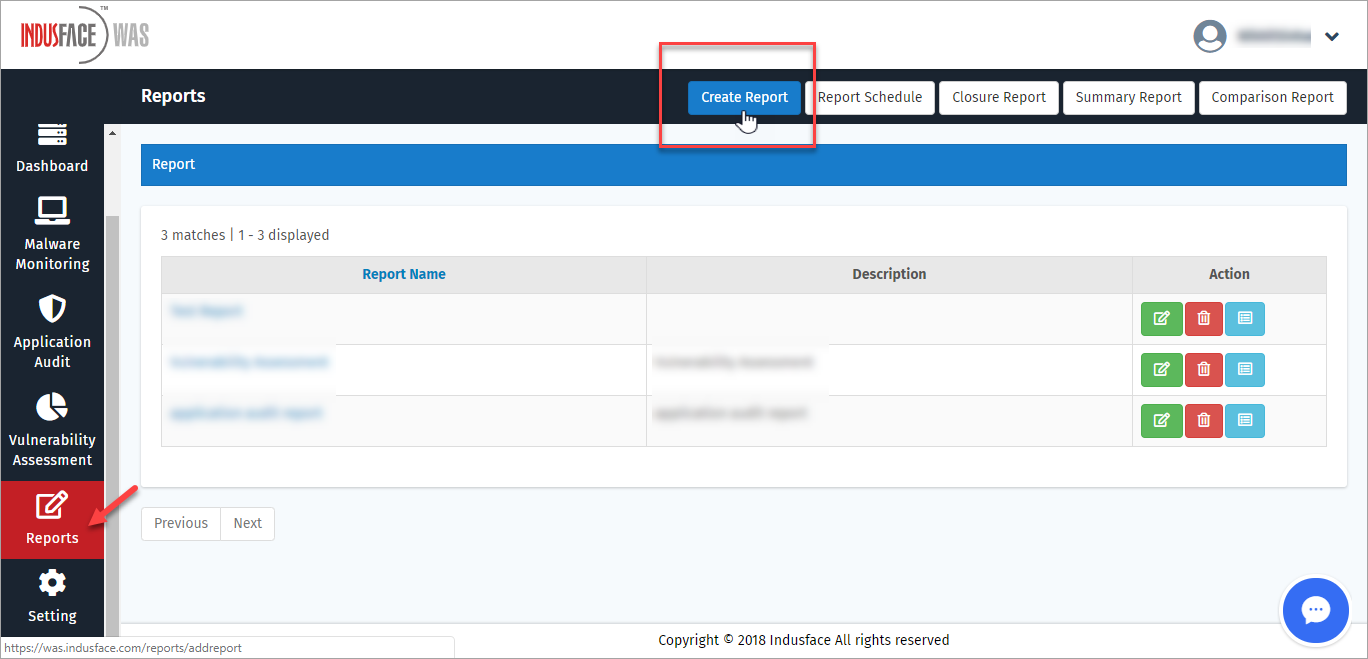
Click here for more information.
How to create a user?
Click User Settings in the Settings tab on the left navigation plane.
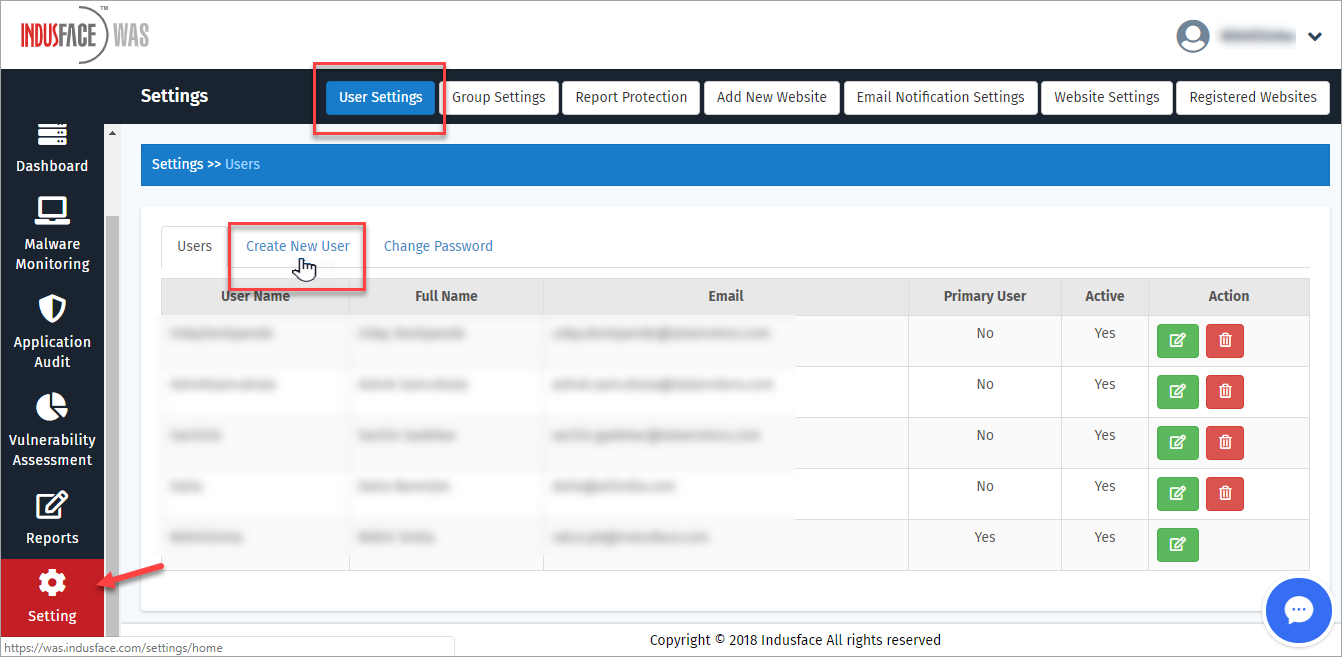
Click here for more information.
How can I change password?
Click Change Password link in the left navigation plane.
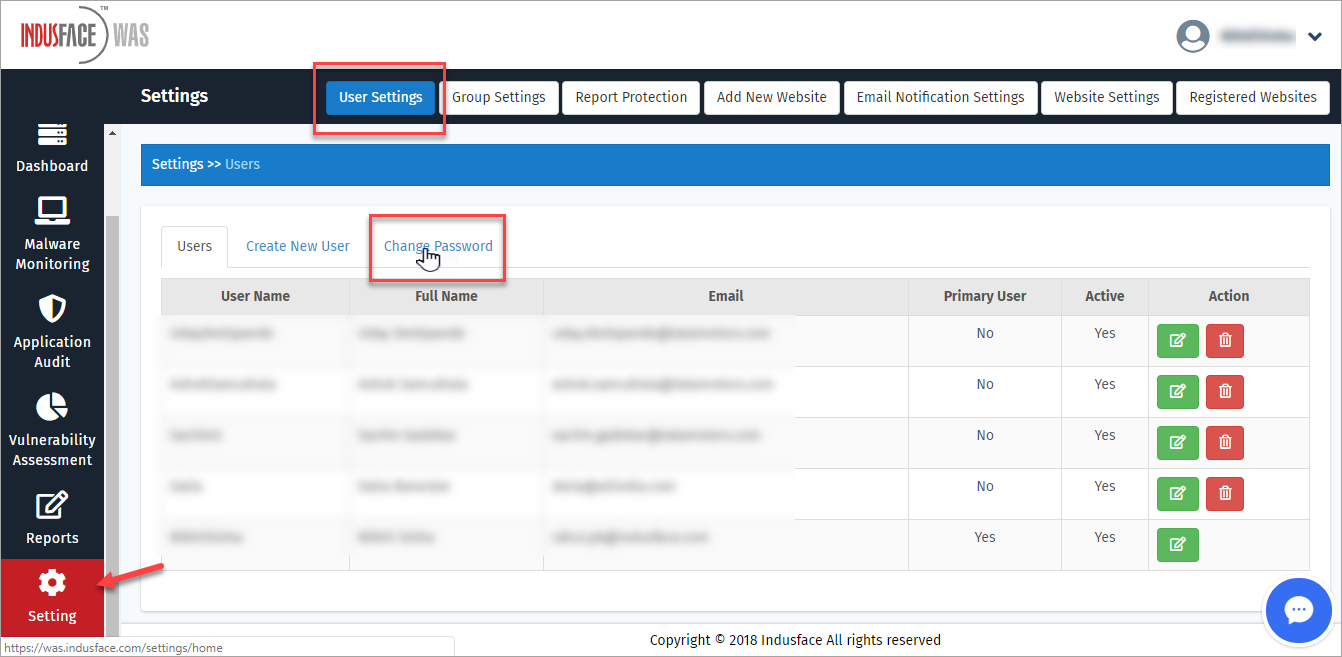
Click here for more information.
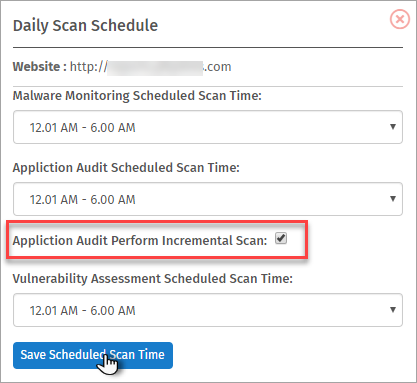
How to schedule a scan?
Various website scan options like Daily Scan, Future Scan etc., can be scheduled.
Click Website Settings option in Settings tab.
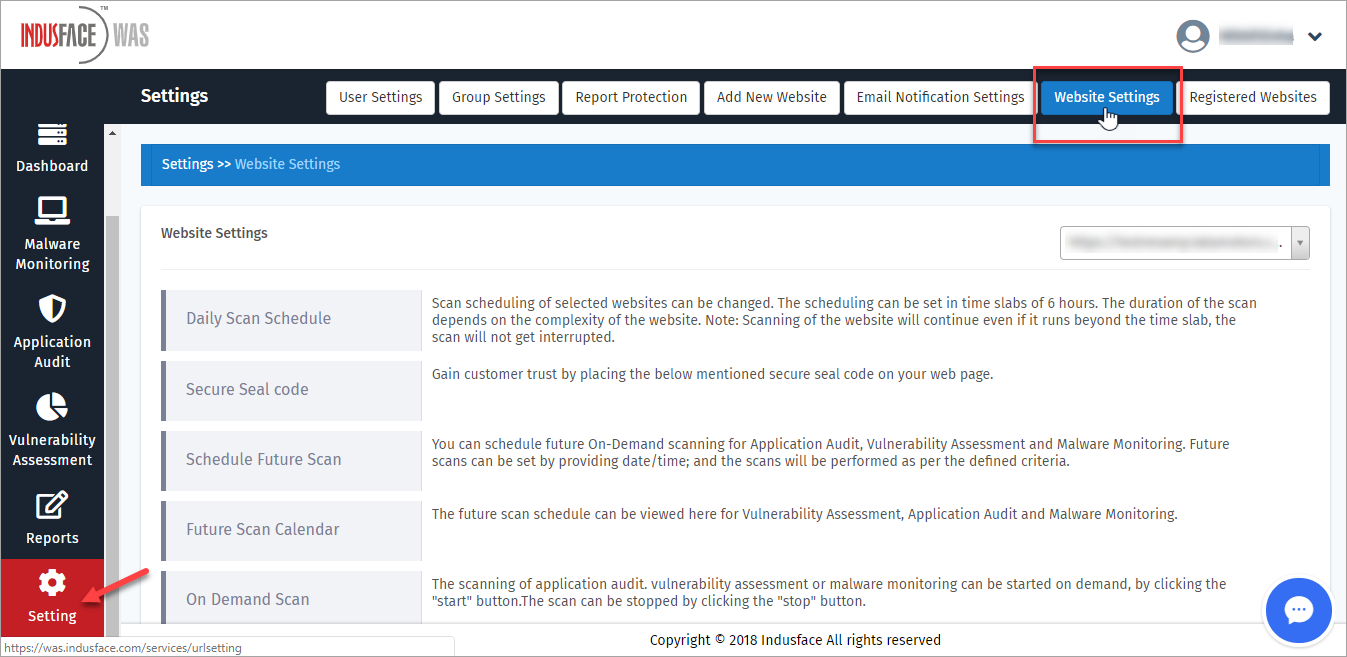
Click here to know more.
My website is too big for one day scan, Is there an option to scan for more than 10 hours? How can I trigger it?
Yes! we have an option to scan bigger websites for 2 or 3 days by pausing the scan instead of stopping or disrupting it.
Click Application Audit Perform Incremental Scan option in Daily Scan Schedule option in Website Settings page.
What is Closure Report? How can I use it?
A Closure report identifies the vulnerabilities that are no longer found in any websites.
Click here to get step by step instructions to create a Closure report.
