AppTrana
Getting Started
Frequently Asked Questions
Product Details
Browser Protection
API Scan Coverage for OWASP Top 10
Malware Scanning for File Uploads
Whitelist Vulnerabilities on the AppTrana WAAP
API Request to Purge CDN Data
Analysis page - Attack Trend Visualisation
Update Origin Server Address
Advanced Behavioral DDoS
BOT Protection
Asset Discovery
Customize Application Behavior with Bot Score
Restricted Admin User
OWASP API Security Top 10 2023 – AppTrana API Protection
Self Service Rules
ASN based IP Whitelisting
Enhance Your API Security with API Classification
SwyftComply for API Scan
Custom Bot Configuration
Configure Custom Error Pages in AppTrana
Configuring Custom Error Page in AppTrana
Enabling SIEM Integration
API Discovery Feature
SwyftComply
Analysis page - Access Trend Visualization
Manage WAAP Email Alerts
Configuring Custom Error and Maintenance Pages in AppTrana WAAP
Enable and Configure Single Sign-On
Origin Health Check Mechanism
WAF Automated Bypass and Unbypass
False Positive Analysis Report on WAAP
DNS Management
Product User Guide
Indusface WAS
Getting Started
Product User Guide
Summary
Dashboard
Malware Monitoring[MM]
Vulnerability Assessment[VA]
Application Audit[AA]
Reports
Settings
Asset Monitoring
New Reporting Structure
API Security Audit
Frequently Asked Questions
Feature Summary
AcuRisQ – Risk Management with Advanced Risk Scoring
Automated API Scanning
WAS Consulting License
API Key Based - Scan Log Export
WAS Defacement Checks
SIEM Integration with Sumo Logic
Indusface WAS Scanned Vulnerabilities
Indusface Newsletter
Indusface Product Newsletter - October 2021
Indusface Product Newsletter- April 2021
Indusface Product Newsletter-January21
Indusface Product Newsletter - June 20
Indusface Product Newsletter - October 19
Indusface Product Newsletter - August 19
Product Newsletter of May 19
Product Newsletter of March 19
Product Newsletter of January 19
WAF Portal Revamp June 18
Product Newsletter of July 18
Product Newsletter of May 18
Product Newsletter of March 18
Product Newsletter of February 18
Product Newsletter of January 18
Indusface Product Newsletter - March 2022
Indusface Product Newsletter - February 2023
Indusface Product Newsletter- October 2022
Zero Day Vulnerability Reports
Vulnerabilities Detected in 2016
CRS vs. Zero Day Vulnerability - December 2016
CRS vs. Zero Day Vulnerability - November 2016
CRS vs. Zero Day Vulnerability - October 2016
CRS vs Zero Day Vulnerability - September 2016
CRS Vs Zero Day Vulnerabilities - August 2016
Vulnerabilities Detected in 2017
Vulnerability Report of April 17
Vulnerability report for Apr 3rd - Apr 9th 17
Vulnerability report for April 17th - Apr 23rd 17
Vulnerability report of April 10th - April 16th
Vulnerability Report of March 17
Vulnerability report for Mar 20th - Mar 26th
Vulnerability report for Mar 13th - Mar 19th
Vulnerability report for 27th Feb - 5th Mar
Vulnerability report for Mar 27th - Apr 2nd
Vulnerability report for Mar 6th - Mar 12th
Vulnerability Report of February 17
Vulnerability Report of January 17
Vulnerability Report of December 17
Vulnerability Report of November 17
Vulnerability Report of August 17
Vulnerability Report of September 17
Vulnerability Report of October 17
Vulnerability Report of July 17
Vulnerability Report of June 17
Vulnerability Report of May 17
Vulnerabilities Detected in 2018
Vulnerability Report of December 18
Vulnerability Report of November 18
Vulnerability Report of October 18
Vulnerability Report of September 18
Vulnerability Report of August 18
Vulnerability Report of July 18
Vulnerability Report of June 18
Vulnerability Reports of May 18
Vulnerability Report of April 18
Vulnerability Report of March 18
Vulnerability Report of February 18
Vulnerability Report of January 18
Vulnerabilities Detected in 2019
Vulnerability Report of December 19
Vulnerability Report of November 19
Vulnerability Report of October 19
Vulnerability Report of September 19
Vulnerability Report of August 19
Vulnerability Report of July 19
Vulnerability Report of June 19
Vulnerability Report of May 19
Vulnerability Report of April 19
Vulnerability Report of March 19
Vulnerability Report of February 19
Vulnerability Report of January 19
vulnerabilities Detected in 2020
Vulnerability Report of December 20
Vulnerability Report of November 20
Vulnerability Report of October 20
Vulnerability Report of Sep 20
Vulnerability Report of July 20
Vulnerability Report of June 20
Vulnerability Report of May 20
Vulnerability Report of April 20
Vulnerability Report of March 20
Vulnerability Report of February 20
Vulnerability Report of January 20
Vulnerabilities Detected in 2021
Vulnerability Report of November 21
Vulnerability Report of October 21
Vulnerability Report of September 21
Vulnerability Report of August 21
Vulnerability Report of July 21
Vulnerability Report of June 21
Vulnerability Report of May 21
Vulnerability Report of April 21
Vulnerability Report of March 21
Vulnerability Report of February 21
Vulnerability Report of January 21
Vulnerability Report of December 21
Vulnerabilities Detected in 2022
Vulnerability Report of January 22
Vulnerability Report of February 22
Vulnerability Report of March 22
Vulnerability Report of April 22
Vulnerability Report of May 22
Vulnerability Report of June 22
Vulnerability Report of July 22
Vulnerability Report of August 22
Vulnerability Report of September 22
Vulnerability Report of October 22
Vulnerability Report of November 22
Zero-Day Vulnerability Report - December 2022
Vulnerabilities Detected in 2023
Vulnerability Report of May 23
Vulnerability Report of March 23
Vulnerability Report of August 23
Vulnerability Report of July 23
Vulnerability Report of April 23
Vulnerability Report of November 23
Vulnerability Report of June 23
Vulnerability Report of December 23
Vulnerability Report of February 23
Vulnerability Report of January 23
Vulnerability Report of September 23
Vulnerability Report of October 23
Vulnerabilities Detected in 2024
Vulnerability Report of October 2024
Vulnerability Report of April 2024
Vulnerability Report of July 2024
Vulnerability Report of May 2024
Vulnerability Report of September 2024
Vulnerability Report of February 2024
Vulnerability Report of December 2024
Vulnerability Report of January 2024
Vulnerability Report of June 2024
Vulnerability Report of March 2024
Vulnerability Report of November 2024
Vulnerability Report of August 2024
Security Bulletin
Vulnerabilities 2024
Hotjar's OAuth+XSS Flaw Exposes Millions at Risk of Account Takeover
Critical Apache OFBiz Zero-day AuthBiz (CVE-2023-49070 and CVE-2023-51467)
CVE-2024-4879 & CVE-2024-5217 Exposed - The Risks of RCE in ServiceNow
ScreenConnect Authentication Bypass (CVE-2024-1709 & CVE-2024-1708)
CVE-2024-4577 – A PHP CGI Argument Injection Vulnerability in Windows Servers
CVE-2024-8517 – Unauthenticated Remote Code Execution in SPIP
CVE-2024-1071 – Critical Vulnerability in Ultimate Member WordPress Plugin
Cryptocurrency Mining Attack Exploiting PHP Vulnerabilities: An Emerging Threat
Oracle WebLogic Server Deserialization
ApacheStructs_VG
Apache Struts 2 Vulnerability CVE-2023-50164 Exposed
Unpacking the Zimbra Cross-Site Scripting Vulnerability(CVE-2023-37580)
Adobe ColdFusion Vulnerabilities Exploited in the Wild
Remote Unauthenticated API Access Vulnerabilities in Ivanti
Multiple Moveit Transfer Vulnerabilities
HTTP/2 Rapid Reset Attack Vulnerability
CVE-2024-9264 - Grafana’s SQL Expressions Vulnerability
CVE-2024-8190 – OS Command Injection in Ivanti CSA
Apache log4j RCE vulnerability
- All Categories
- Security Bulletin
- Vulnerabilities 2024
- CVE-2024-4577 – A PHP CGI Argument Injection Vulnerability in Windows Servers
CVE-2024-4577 – A PHP CGI Argument Injection Vulnerability in Windows Servers
Updated
by vinugayathri.chinnasamy@indusface.com
On June 7, 2024, a new critical PHP vulnerability CVE-2024-4577 was revealed, mainly impacting XAMPP on Windows. It happens when PHP runs in CGI mode with specific language settings, like Chinese or Japanese.
The problem comes from how PHP handles certain characters, allowing attackers to inject code through web requests and take control of servers.
This vulnerability, if exploited, could lead to the execution of arbitrary code, a scenario with severe consequences for system integrity and data security.
Insights and Analysis- CVE-2024-4577
CVE-2024-4577 signifies a CGI argument injection vulnerability within PHP, capable of compromising Windows-based servers running PHP.
Risk Analysis
Severity: Critical CVSSv3.x: Base Score: 9.8 Critical
Vector: CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H CVSSv2: Base Score: 7.5 High Vector: CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P
Exploit available in public: Yes Exploit complexity: Low
The vulnerability impacts:
- PHP 8.3 versions earlier than 8.3.8
- PHP 8.2 versions earlier than 8.2.20
- PHP 8.1 versions earlier than 8.1.29
These versions, if left unpatched, remain susceptible to exploitation, leaving servers vulnerable to unauthorized access and potential data breaches.
The vulnerability traces its roots to errors in character encoding conversions, particularly within the "Best Fit" feature on Windows systems. This oversight provides attackers with a loophole to bypass existing security measures, notably those designed to thwart CVE-2012-1823, a predecessor vulnerability.
Active Exploitation
Hackers try to exploit the vulnerability within a day of its disclosure. The availability of proof-of-concept (PoC) attack code and active scans online underscores the urgency to apply immediate patches.
Attackers are exploiting CVE-2024–4577 in different ways with two primary attack scenarios emerging:
· CGI Mode Exploitation:
This vulnerability can be directly exploited when configuring the Action directive in Apache HTTP Server to map HTTP requests to a PHP-CGI executable binary.
· XAMPP Vulnerability:
The default configuration of XAMPP, a widely used PHP development environment, is susceptible to exploitation. Even if PHP is not configured in CGI mode, simply exposing the PHP executable binary in the CGI directory makes it vulnerable.
Common examples include copying php.exe or php-cgi.exe to the /cgi-bin/ directory.
Mitigation Strategies
Mitigating CVE-2024-4577 requires a multi-faceted approach, involving proactive measures and timely patching. Key mitigation strategies include:
· Immediate Patching: System admins should quickly update PHP installations to the patched versions (8.3.8, 8.2.20, and 8.1.29) provided by the PHP Group.
· Disabling CGI Features: In vulnerable environments like XAMPP, disabling PHP CGI features mitigates the risk of exploitation.
· Modifying Server Configurations: Employing mod_rewrite rules can enhance server defenses against potential exploits, augmenting existing security measures.
· Rewrite Rules: For users who cannot upgrade PHP can use these Rewrite Rules to block attacks temporarily.
AppTrana WAAP Coverage for CVE-2024-4577
AppTrana WAAP ensures that our customers are shielded from the risks associated with CVE-2024-4577 and similar vulnerabilities from Day 0.
In addition to relying on patches from the software vendor, the Indusface managed security team has developed rules specifically designed to swiftly detect injection vulnerabilities in PHP and prevent exploitation attempts.
Rule ID | Category |
124 | PHP Injection Attacks Policy |
99876 | PHP Injection Attacks Policy |
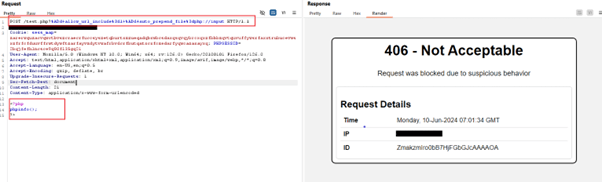
WAAP effectively blocks potential attacks by issuing a robust 406-status code
AppTrana WAAP has a proven track record of safeguarding organizations from cyber-attacks by addressing both zero-day exploits and known vulnerabilities at the earliest stages.
Leveraging the expertise of our managed service team, along with built-in DAST Scanner and autonomous patching capabilities, AppTrana WAAP ensures that our customers remain protected from both new and existing exploits.
