AppTrana
Getting Started
Frequently Asked Questions
Product Details
Browser Protection
API Scan Coverage for OWASP Top 10
Malware Scanning for File Uploads
Whitelist Vulnerabilities on the AppTrana WAAP
API Request to Purge CDN Data
Analysis page - Attack Trend Visualisation
Update Origin Server Address
Advanced Behavioral DDoS
BOT Protection
Asset Discovery
Customize Application Behavior with Bot Score
Restricted Admin User
OWASP API Security Top 10 2023 – AppTrana API Protection
Self Service Rules
ASN based IP Whitelisting
Enhance Your API Security with API Classification
SwyftComply for API Scan
Custom Bot Configuration
Configure Custom Error Pages in AppTrana
Configuring Custom Error Page in AppTrana
Enabling SIEM Integration
API Discovery Feature
SwyftComply
Analysis page - Access Trend Visualization
Manage WAAP Email Alerts
Configuring Custom Error and Maintenance Pages in AppTrana WAAP
Enable and Configure Single Sign-On
Origin Health Check Mechanism
WAF Automated Bypass and Unbypass
False Positive Analysis Report on WAAP
DNS Management
Product User Guide
Indusface WAS
Getting Started
Product User Guide
Summary
Dashboard
Malware Monitoring[MM]
Vulnerability Assessment[VA]
Application Audit[AA]
Reports
Settings
Asset Monitoring
New Reporting Structure
API Security Audit
Frequently Asked Questions
Feature Summary
AcuRisQ – Risk Management with Advanced Risk Scoring
Automated API Scanning
WAS Consulting License
API Key Based - Scan Log Export
WAS Defacement Checks
SIEM Integration with Sumo Logic
Indusface WAS Scanned Vulnerabilities
Indusface Newsletter
Indusface Product Newsletter - October 2021
Indusface Product Newsletter- April 2021
Indusface Product Newsletter-January21
Indusface Product Newsletter - June 20
Indusface Product Newsletter - October 19
Indusface Product Newsletter - August 19
Product Newsletter of May 19
Product Newsletter of March 19
Product Newsletter of January 19
WAF Portal Revamp June 18
Product Newsletter of July 18
Product Newsletter of May 18
Product Newsletter of March 18
Product Newsletter of February 18
Product Newsletter of January 18
Indusface Product Newsletter - March 2022
Indusface Product Newsletter - February 2023
Indusface Product Newsletter- October 2022
Zero Day Vulnerability Reports
Vulnerabilities Detected in 2016
CRS vs. Zero Day Vulnerability - December 2016
CRS vs. Zero Day Vulnerability - November 2016
CRS vs. Zero Day Vulnerability - October 2016
CRS vs Zero Day Vulnerability - September 2016
CRS Vs Zero Day Vulnerabilities - August 2016
Vulnerabilities Detected in 2017
Vulnerability Report of April 17
Vulnerability report for Apr 3rd - Apr 9th 17
Vulnerability report for April 17th - Apr 23rd 17
Vulnerability report of April 10th - April 16th
Vulnerability Report of March 17
Vulnerability report for Mar 20th - Mar 26th
Vulnerability report for Mar 13th - Mar 19th
Vulnerability report for 27th Feb - 5th Mar
Vulnerability report for Mar 27th - Apr 2nd
Vulnerability report for Mar 6th - Mar 12th
Vulnerability Report of February 17
Vulnerability Report of January 17
Vulnerability Report of December 17
Vulnerability Report of November 17
Vulnerability Report of August 17
Vulnerability Report of September 17
Vulnerability Report of October 17
Vulnerability Report of July 17
Vulnerability Report of June 17
Vulnerability Report of May 17
Vulnerabilities Detected in 2018
Vulnerability Report of December 18
Vulnerability Report of November 18
Vulnerability Report of October 18
Vulnerability Report of September 18
Vulnerability Report of August 18
Vulnerability Report of July 18
Vulnerability Report of June 18
Vulnerability Reports of May 18
Vulnerability Report of April 18
Vulnerability Report of March 18
Vulnerability Report of February 18
Vulnerability Report of January 18
Vulnerabilities Detected in 2019
Vulnerability Report of December 19
Vulnerability Report of November 19
Vulnerability Report of October 19
Vulnerability Report of September 19
Vulnerability Report of August 19
Vulnerability Report of July 19
Vulnerability Report of June 19
Vulnerability Report of May 19
Vulnerability Report of April 19
Vulnerability Report of March 19
Vulnerability Report of February 19
Vulnerability Report of January 19
vulnerabilities Detected in 2020
Vulnerability Report of December 20
Vulnerability Report of November 20
Vulnerability Report of October 20
Vulnerability Report of Sep 20
Vulnerability Report of July 20
Vulnerability Report of June 20
Vulnerability Report of May 20
Vulnerability Report of April 20
Vulnerability Report of March 20
Vulnerability Report of February 20
Vulnerability Report of January 20
Vulnerabilities Detected in 2021
Vulnerability Report of November 21
Vulnerability Report of October 21
Vulnerability Report of September 21
Vulnerability Report of August 21
Vulnerability Report of July 21
Vulnerability Report of June 21
Vulnerability Report of May 21
Vulnerability Report of April 21
Vulnerability Report of March 21
Vulnerability Report of February 21
Vulnerability Report of January 21
Vulnerability Report of December 21
Vulnerabilities Detected in 2022
Vulnerability Report of January 22
Vulnerability Report of February 22
Vulnerability Report of March 22
Vulnerability Report of April 22
Vulnerability Report of May 22
Vulnerability Report of June 22
Vulnerability Report of July 22
Vulnerability Report of August 22
Vulnerability Report of September 22
Vulnerability Report of October 22
Vulnerability Report of November 22
Zero-Day Vulnerability Report - December 2022
Vulnerabilities Detected in 2023
Vulnerability Report of May 23
Vulnerability Report of March 23
Vulnerability Report of August 23
Vulnerability Report of July 23
Vulnerability Report of April 23
Vulnerability Report of November 23
Vulnerability Report of June 23
Vulnerability Report of December 23
Vulnerability Report of February 23
Vulnerability Report of January 23
Vulnerability Report of September 23
Vulnerability Report of October 23
Vulnerabilities Detected in 2024
Vulnerability Report of October 2024
Vulnerability Report of April 2024
Vulnerability Report of July 2024
Vulnerability Report of May 2024
Vulnerability Report of September 2024
Vulnerability Report of February 2024
Vulnerability Report of December 2024
Vulnerability Report of January 2024
Vulnerability Report of June 2024
Vulnerability Report of March 2024
Vulnerability Report of November 2024
Vulnerability Report of August 2024
Security Bulletin
Vulnerabilities 2024
Hotjar's OAuth+XSS Flaw Exposes Millions at Risk of Account Takeover
Critical Apache OFBiz Zero-day AuthBiz (CVE-2023-49070 and CVE-2023-51467)
CVE-2024-4879 & CVE-2024-5217 Exposed - The Risks of RCE in ServiceNow
ScreenConnect Authentication Bypass (CVE-2024-1709 & CVE-2024-1708)
CVE-2024-4577 – A PHP CGI Argument Injection Vulnerability in Windows Servers
CVE-2024-8517 – Unauthenticated Remote Code Execution in SPIP
CVE-2024-1071 – Critical Vulnerability in Ultimate Member WordPress Plugin
Cryptocurrency Mining Attack Exploiting PHP Vulnerabilities: An Emerging Threat
Oracle WebLogic Server Deserialization
ApacheStructs_VG
Apache Struts 2 Vulnerability CVE-2023-50164 Exposed
Unpacking the Zimbra Cross-Site Scripting Vulnerability(CVE-2023-37580)
Adobe ColdFusion Vulnerabilities Exploited in the Wild
Remote Unauthenticated API Access Vulnerabilities in Ivanti
Multiple Moveit Transfer Vulnerabilities
HTTP/2 Rapid Reset Attack Vulnerability
CVE-2024-9264 - Grafana’s SQL Expressions Vulnerability
CVE-2024-8190 – OS Command Injection in Ivanti CSA
Apache log4j RCE vulnerability
Table of Contents
- All Categories
- Security Bulletin
- Vulnerabilities 2024
- CVE-2024-8517 – Unauthenticated Remote Code Execution in SPIP
CVE-2024-8517 – Unauthenticated Remote Code Execution in SPIP
 Updated
by Rama Sadhu
Updated
by Rama Sadhu
A critical security flaw has been discovered in SPIP, a popular open-source content management system (CMS). This flaw, identified as CVE-2024-8517, stems from a command injection issue in the BigUp plugin. The vulnerability allows attackers to execute arbitrary OS commands remotely and without authentication, simply by sending a malicious multipart file upload HTTP request.
This blog will explore the details of this vulnerability, its potential impacts, and the essential steps for mitigation.
CVE-2024-8517 – SPIP BigUp Plugin – RCE
Risk Analysis
Severity: High
CVSSv3.1: Base Score:9.8 Critical
CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
Exploit available in public: No
Exploit complexity: Low
CVE-2024-8517 arises from improper handling of user inputs in the lister_fichiers_par_champs function. This function fails to adequately sanitize data from file uploads, particularly when the bigup_retrouver_fichiers parameter is set to 1. As a result, attackers can craft malicious HTTP requests containing harmful PHP code, which, when processed, executes arbitrary commands on the server.
The vulnerability affects all versions of SPIP before 4.3.2, 4.2.16, and 4.1.18.
One of the most alarming aspects of this vulnerability is its unauthenticated nature. Attackers do not need any special privileges or access to exploit it; they can perform the attack by simply sending a specially crafted HTTP request to the affected SPIP server which increases more chances of exploitation.
Impact
The vulnerability allows remote code execution, potentially leading to:
- Unauthorized Access to Sensitive Data: Attackers could gain access to confidential information stored on the server.
- Modification or Deletion of Critical Files: The integrity of critical system files could be compromised.
- Installation of Malware: Attackers may install malicious software or backdoors on the server.
- Lateral Movement: The compromised system could serve as a foothold for further attacks within the network.
- System as a Launching Point: The server could be used as a base for additional attacks targeting other systems.
While it has not yet been observed in the wild, the publication of a proof-of-concept (PoC) exploit increases the likelihood of it being used in real-world attacks.
Mitigation Strategies
To mitigate the risks associated with CVE-2024-8517, it is crucial to update to the latest patched versions: 4.3.2 or later for the 4.3.x branch, 4.2.16 or later for the 4.2.x branch, and 4.1.18 or later for the 4.1.x branch.
Also consider implementing the following additional mitigations:
- Restrict Access: Limit the file upload functionality to trusted users only.
- Enhance Input Validation: Apply strict input validation and sanitization for all file uploads.
- Monitor Logs: Regularly check system logs for any unusual activity related to file uploads or command execution.
- Conduct a Security Audit: Perform a thorough security audit of affected systems to ensure no compromise has occurred.
- Strengthen Security Practices: Review and enhance overall security measures, especially those related to file uploads and command execution prevention.
- Deploy a WAF: Utilize a Web Application Firewall (WAF) to filter potentially malicious requests.
AppTrana Coverage on RCE Vulnerabilities
With AppTrana WAAP, our customers are shielded from RCE exploits, including CVE-2024–8417, right from Day 0.
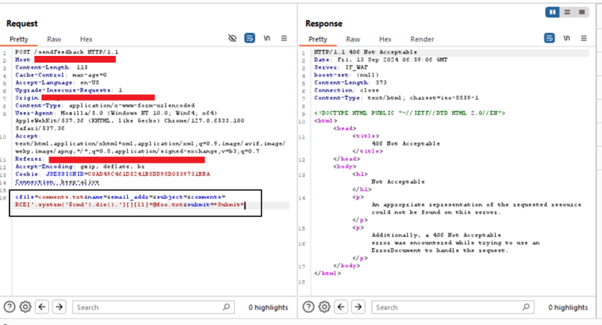
The screenshots illustrate AppTrana WAAP’s capability to effectively block this vulnerability. When malicious requests are intercepted by Burp, WAAP responds promptly with a firm 406-status code.
1)name= “HELLO[AB’.system(‘id’).die().’CD]”
![CVE-2024-8517 - AppTrana WAAP Coverage - command injection PoC using the payload HELLO[AB'.system('id').die().'CD]](https://www.indusface.com/wp-content/uploads/2024/09/CVE-2024-8517-AppTrana-WAAP-Coverage-PoC-1.png)
2) name=”RCE’-system(‘id’)-‘[ABCD]”
![command injection PoC using the payload ) name="RCE'-system('id')-'[ABCD]"](https://www.indusface.com/wp-content/uploads/2024/09/CVE-2024-8517-AppTrana-WAAP-Coverage-PoC-2.png)
3) name=”RCE’-sprintf(system(‘id’),die())-‘[ABCD]”
![command injection PoC using the payload name="RCE'-sprintf(system('id'),die())-'[ABCD]"](https://www.indusface.com/wp-content/uploads/2024/09/CVE-2024-8517-AppTrana-WAAP-Coverage-PoC-3.png)
4) name:RCE[‘.system(‘$cmd’).die().’][][ll]=@foo.txt