AppTrana
Getting Started
Frequently Asked Questions
Product Details
API Scan Coverage for OWASP Top 10
Whitelist Vulnerabilities on the AppTrana WAAP
API Request to Purge CDN Data
Analysis page - Attack Trend Visualisation
Advanced Behavioral DDoS
BOT Protection
Asset Discovery
Customize Application Behavior with Bot Score
Restricted Admin User
Self Service Rules
Configuring Custom Error Page in AppTrana
Enabling SIEM Integration
API Discovery Feature
SwyftComply
Analysis page - Access Trend Visualization
Manage WAAP Email Alerts
Enable and Configure Single Sign-On
WAF Automated Bypass and Unbypass
False Positive Analysis Report on WAAP
Product User Guide
Indusface WAS
Getting Started
Product User Guide
Summary
Dashboard
Malware Monitoring[MM]
Application Audit[AA]
Vulnerability Assessment[VA]
Reports
Settings
Asset Monitoring
New Reporting Structure
Frequently Asked Questions
Feature Summary
AcuRisQ – Risk Management with Advanced Risk Scoring
WAS Consulting License
API Key Based - Scan Log Export
WAS Defacement Checks
SIEM Integration with Sumo Logic
Indusface WAS Scanned Vulnerabilities
Total Application Security
Onboarding Documents
Indusface Newsletter
Indusface Product Newsletter - October 2021
Indusface Product Newsletter- April 2021
Indusface Product Newsletter-January21
Indusface Product Newsletter - June 20
Indusface Product Newsletter - October 19
Indusface Product Newsletter - August 19
Product Newsletter of May 19
Product Newsletter of March 19
Product Newsletter of January 19
WAF Portal Revamp June 18
Product Newsletter of July 18
Product Newsletter of May 18
Product Newsletter of March 18
Product Newsletter of February 18
Product Newsletter of January 18
Indusface Product Newsletter - March 2022
Indusface Product Newsletter - February 2023
Indusface Product Newsletter- October 2022
Zero Day Vulnerability Reports
Vulnerabilities Detected in 2023
Vulnerability Report of May 23
Vulnerability Report of March 23
Vulnerability Report of August 23
Vulnerability Report of July 23
Vulnerability Report of April 23
Vulnerability Report of November 23
Vulnerability Report of June 23
Vulnerability Report of December 23
Vulnerability Report of February 23
Vulnerability Report of January 23
Vulnerability Report of September 23
Vulnerability Report of October 23
Vulnerabilities Detected in 2016
CRS vs. Zero Day Vulnerability - December 2016
CRS vs. Zero Day Vulnerability - November 2016
CRS vs. Zero Day Vulnerability - October 2016
CRS vs Zero Day Vulnerability - September 2016
CRS Vs Zero Day Vulnerabilities - August 2016
Vulnerabilities Detected in 2017
Vulnerability Report of April 17
Vulnerability report for Apr 3rd - Apr 9th 17
Vulnerability report for April 17th - Apr 23rd 17
Vulnerability report of April 10th - April 16th
Vulnerability Report of March 17
Vulnerability report for Mar 20th - Mar 26th
Vulnerability report for Mar 13th - Mar 19th
Vulnerability report for 27th Feb - 5th Mar
Vulnerability report for Mar 27th - Apr 2nd
Vulnerability report for Mar 6th - Mar 12th
Vulnerability Report of February 17
Vulnerability Report of January 17
Vulnerability Report of December 17
Vulnerability Report of November 17
Vulnerability Report of August 17
Vulnerability Report of September 17
Vulnerability Report of October 17
Vulnerability Report of July 17
Vulnerability Report of June 17
Vulnerability Report of May 17
Vulnerabilities Detected in 2018
Vulnerability Report of December 18
Vulnerability Report of November 18
Vulnerability Report of October 18
Vulnerability Report of September 18
Vulnerability Report of August 18
Vulnerability Report of July 18
Vulnerability Report of June 18
Vulnerability Reports of May 18
Vulnerability Report of April 18
Vulnerability Report of March 18
Vulnerability Report of February 18
Vulnerability Report of January 18
Vulnerabilities Detected in 2019
Vulnerability Report of December 19
Vulnerability Report of November 19
Vulnerability Report of October 19
Vulnerability Report of September 19
Vulnerability Report of August 19
Vulnerability Report of July 19
Vulnerability Report of June 19
Vulnerability Report of May 19
Vulnerability Report of April 19
Vulnerability Report of March 19
Vulnerability Report of February 19
Vulnerability Report of January 19
vulnerabilities Detected in 2020
Vulnerability Report of December 20
Vulnerability Report of November 20
Vulnerability Report of October 20
Vulnerability Report of Sep 20
Vulnerability Report of July 20
Vulnerability Report of June 20
Vulnerability Report of May 20
Vulnerability Report of April 20
Vulnerability Report of March 20
Vulnerability Report of February 20
Vulnerability Report of January 20
Vulnerabilities Detected in 2021
Vulnerability Report of November 21
Vulnerability Report of October 21
Vulnerability Report of September 21
Vulnerability Report of August 21
Vulnerability Report of July 21
Vulnerability Report of June 21
Vulnerability Report of May 21
Vulnerability Report of April 21
Vulnerability Report of March 21
Vulnerability Report of February 21
Vulnerability Report of January 21
Vulnerability Report of December 21
Vulnerabilities Detected in 2022
Vulnerability Report of January 22
Vulnerability Report of February 22
Vulnerability Report of March 22
Vulnerability Report of April 22
Vulnerability Report of May 22
Vulnerability Report of June 22
Vulnerability Report of July 22
Vulnerability Report of August 22
Vulnerability Report of September 22
Vulnerability Report of October 22
Vulnerability Report of November 22
Zero-Day Vulnerability Report - December 2022
Vulnerabilities Detected in 2024
Security Bulletin
Vulnerabilities 2024
Critical Apache OFBiz Zero-day AuthBiz (CVE-2023-49070 and CVE-2023-51467)
ScreenConnect Authentication Bypass (CVE-2024-1709 & CVE-2024-1708)
CVE-2024-1071 – Critical Vulnerability in Ultimate Member WordPress Plugin
Oracle WebLogic Server Deserialization
ApacheStructs_VG
Apache Struts 2 Vulnerability CVE-2023-50164 Exposed
Unpacking the Zimbra Cross-Site Scripting Vulnerability(CVE-2023-37580)
Adobe ColdFusion Vulnerabilities Exploited in the Wild
Remote Unauthenticated API Access Vulnerabilities in Ivanti
Multiple Moveit Transfer Vulnerabilities
HTTP/2 Rapid Reset Attack Vulnerability
Apache log4j RCE vulnerability
Table of Contents
- All Categories
- Total Application Security
- Onboarding Documents
- Marketplace
- How to Setup Total Application Security
- Apptrana Login after TAS Configuration
Apptrana Login after TAS Configuration
Updated
by Author
Existing AWS Customer
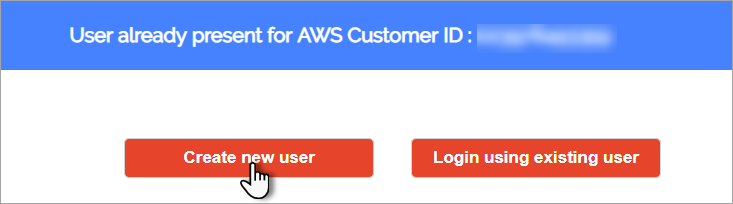
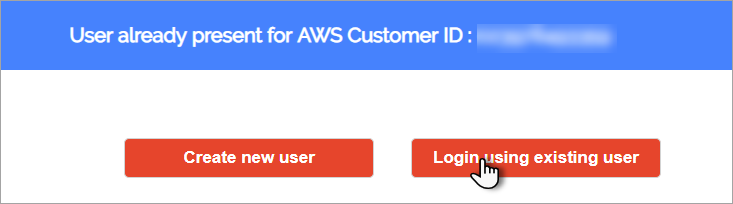
As a user is already present for AWS Customer ID, two options i.e., Create new user and Login using existing user options appear.
Create New User
Click Create new user button to create new user for existing aws customer. Add New User page appears.
Enter the details in respective fields and click Register button. Apptrana Login page appears.
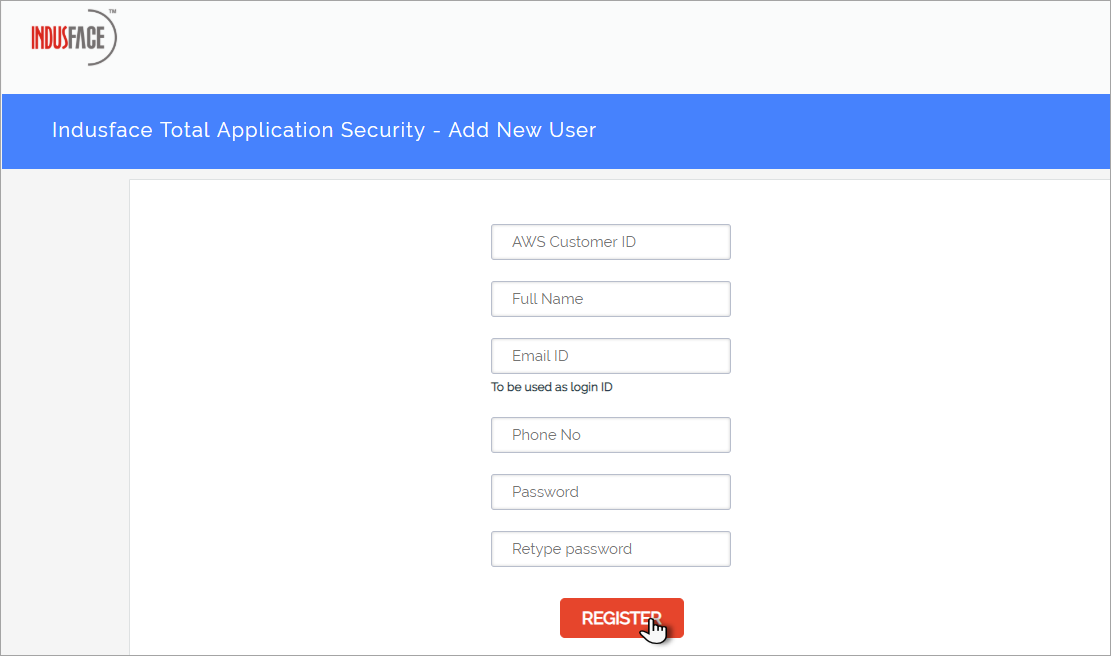
Parameter | Description |
AWS Customer ID | Copy your AWS ID i.e., given as Owner in Instance details. |
Full Name | Enter your full name in this field. |
Email ID | Enter your official Email ID in this field. |
Phone No | Click to enter your contact information. |
Password | Create a password as per Indusface password policy. |
Retype password | Re-enter your password to confirm your password. |
With successful entry of user details, Apptrana Login page appears.
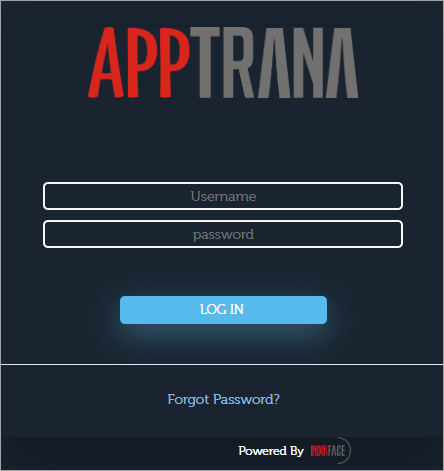
Enter the respective details and click Log In button. Indusface Terms of Services pop-up appears.
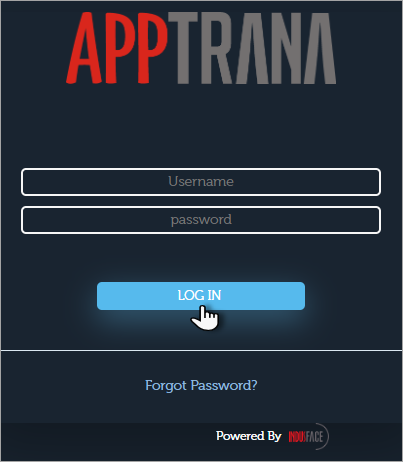
Parameter | Description |
Username | Click and copy your AWS Customer ID as username. |
Password | Click and copy your Instance ID as password. Password can be updated as per user requirement once logged in as per our Password Policy. Click here for more info on update password. |
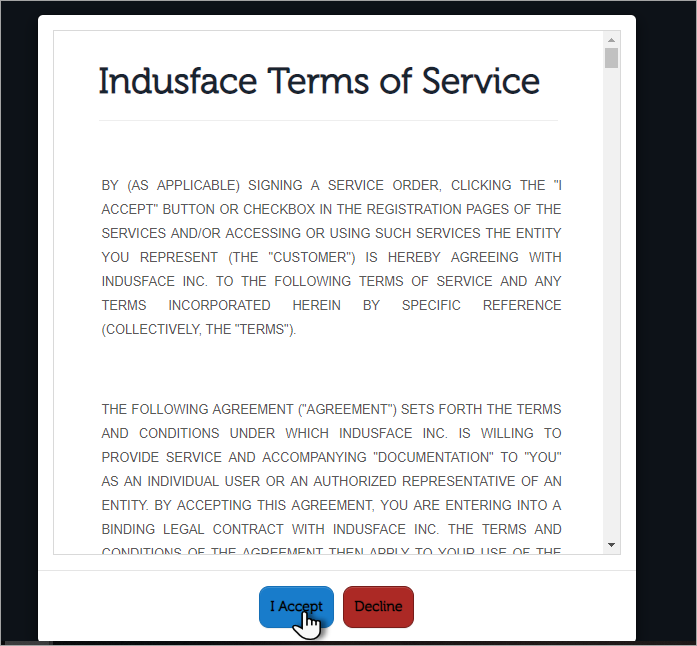
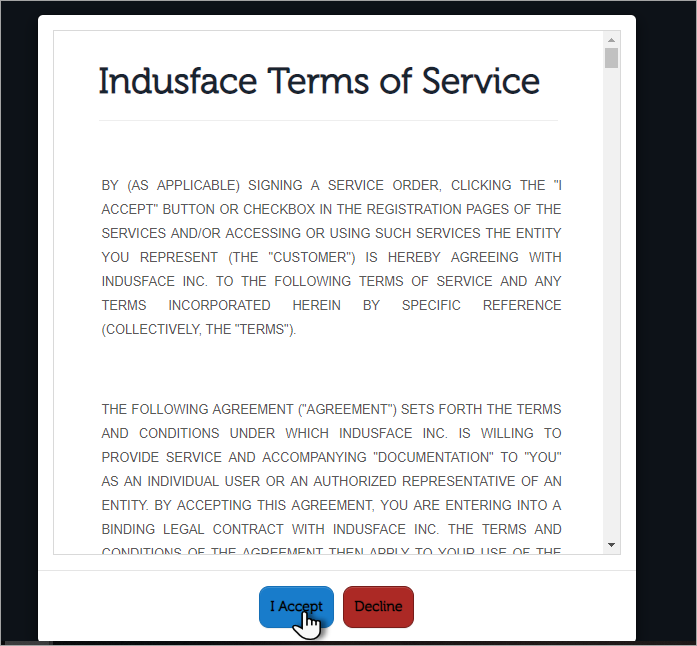
With successful entry of login credentials, Indusface terms of services page appears.
Click I Accept button to login to Apptrana by agreeing to Indusface Terms. Apptrana Dashboard page appears.
Apptrana is designed to address the shortcomings in existing cloud security solutions based on your existing risk posture as we Detect your risks continuously, Protect your application immediately, ensure round-the-clock availability, improve website performance instantly, 360 degrees view of your application security etc.
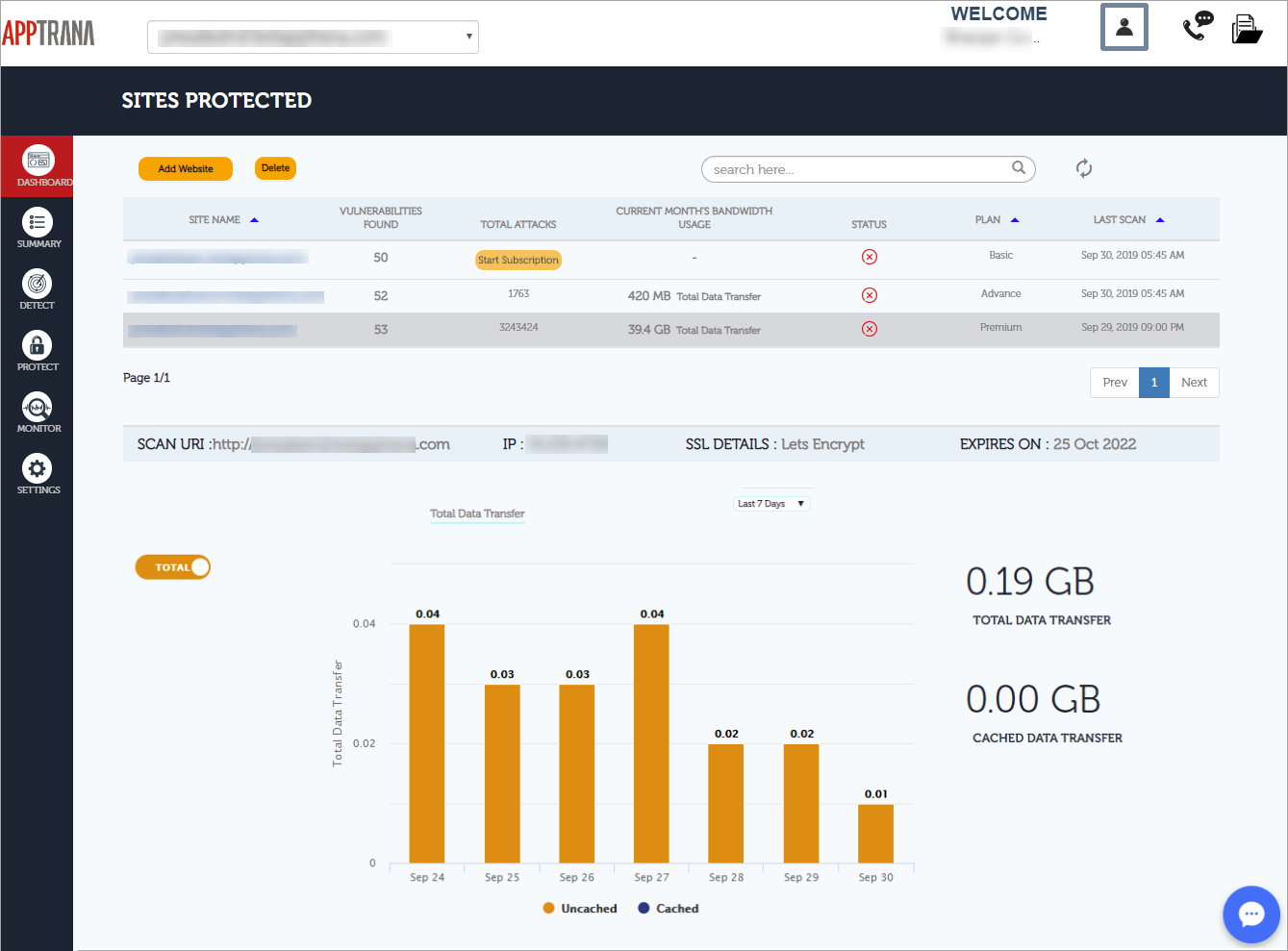
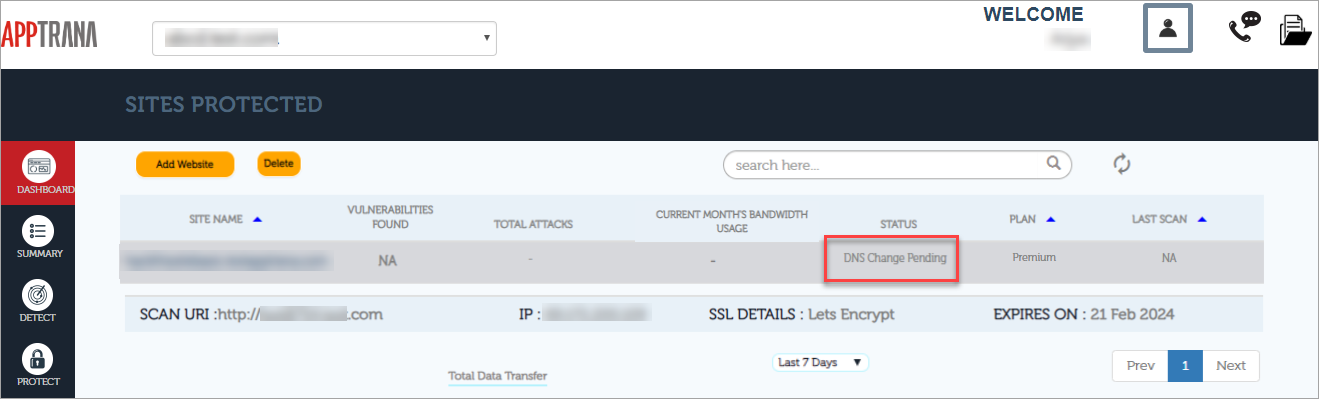
Dashboard or Sites Protected page appears as an entry point of Apptrana portal. No data is visible as the domain is just onboarded. An auto-scan will be in progress with successful configuration.
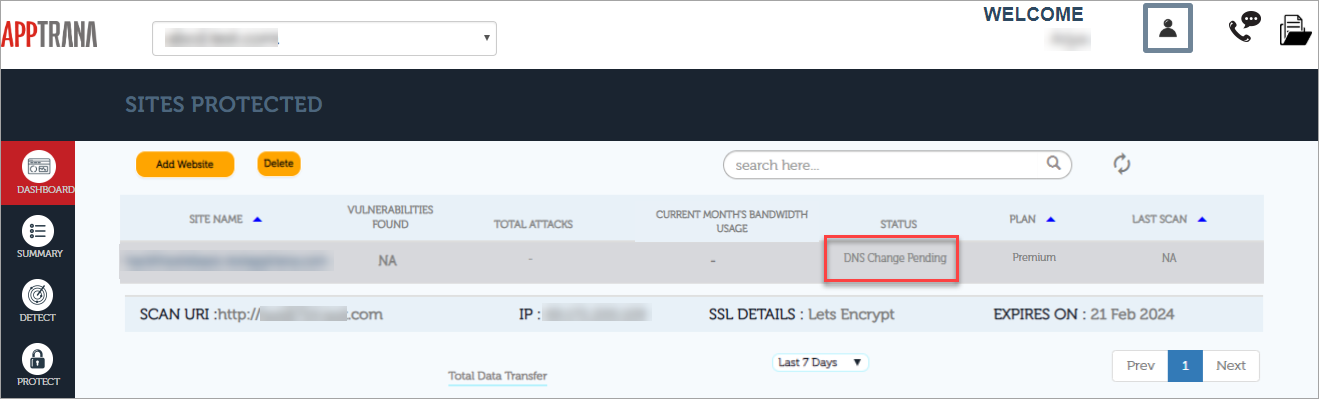
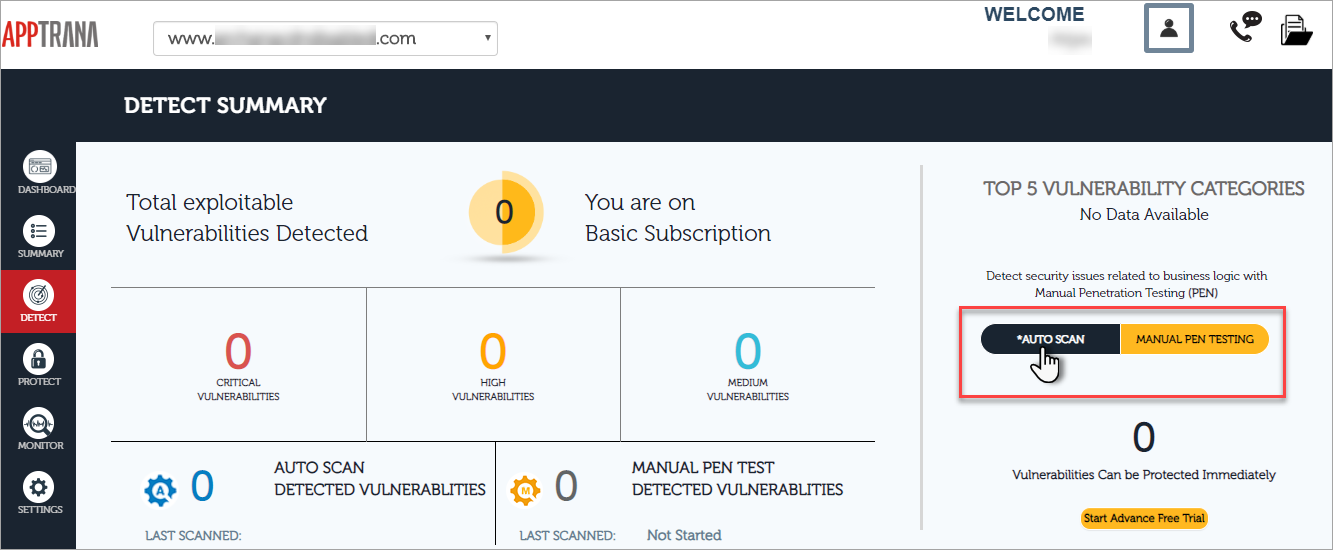
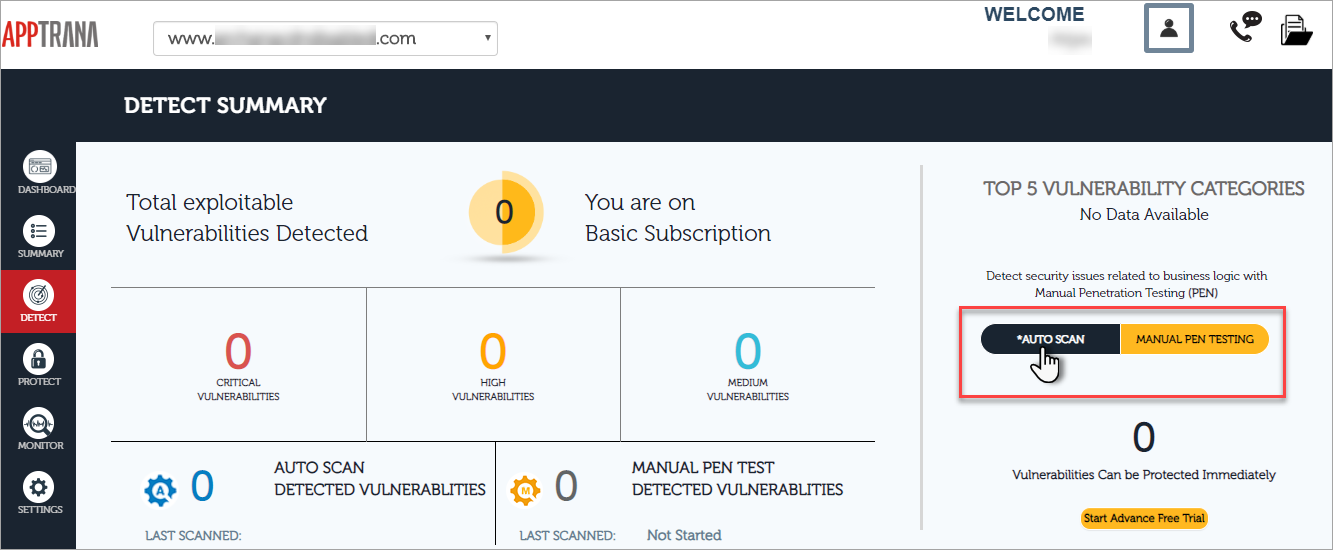
Once the DNS change is successful, an auto-scan will begin and it can be viewed in Detect page. If auto-scan is not started, click Auto-scan button in Detect Summary page.
We suggest you to perform Manual Pen Testing as our experts get right into detecting for any business logic vulnerabilities and other vulnerabilities with logical testing.
Go through our Apptrana Docs on each page of Apptrana portal as we get into each detail of features.
Login Using Existing User
Click Login using existing user button to use the existing user details. Apptrana Login page appears.
Click Username and Password fields, enter the respective details and then click Log in button. Dashboard pop-up appears.
The existing customer details are displayed. Total Data Transfer and Cached Data Transfer graphs are displayed for last 7 days, last 30 days and last month. Further details like Vulnerabilities found, Total attacks, Bandwidth used in last 30 days etc.
Go through our Apptrana Docs on each page of Apptrana portal as we get into the details of each feature.
New AWS Customer
Add New User page appears with registration details. Enter the details in respective fields and click Register button. Apptrana Login page appears.
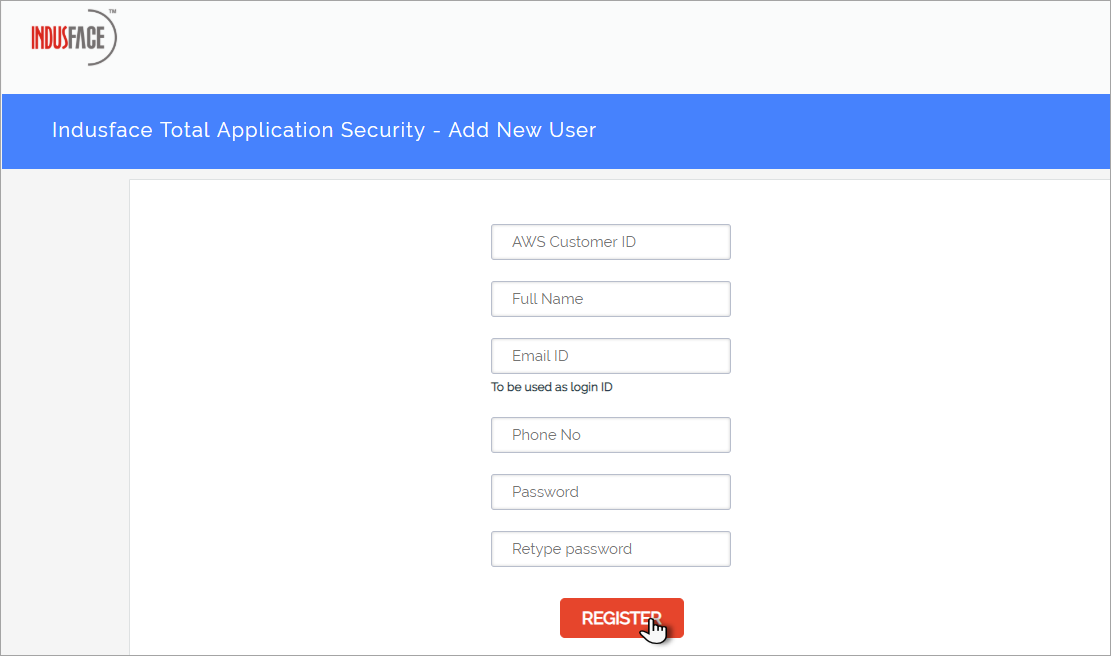
Parameter | Description |
AWS Customer ID | Copy your AWS ID i.e., given as Owner in Instance details. |
Full Name | Enter your full name in this field. |
Email ID | Enter your official Email ID in this field. |
Phone No | Click to enter your contact information. |
Password | Create a password as per Indusface password policy. |
Retype password | Re-enter your password to confirm your password. |
With successful entry of user details, Apptrana Login page appears.
Click Username and Password fields, enter the respective details and then click Log in button. Indusface Terms of Services pop-up appears.
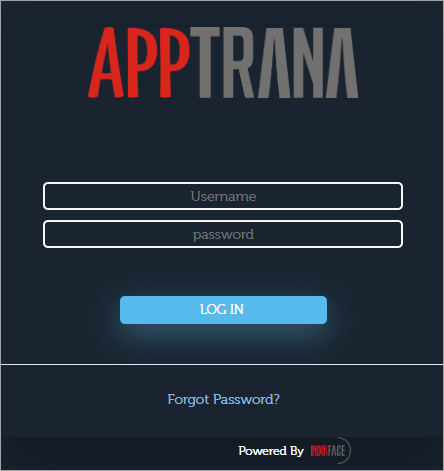
Parameter | Description |
Username | click and copy your AWS Customer ID as username. |
Password | Click and copy your Instance ID as password. |
With successful entry of login credentials, Indusface terms of services page appears.
Click I Accept button to login to Apptrana by agreeing to Indusface Terms. Apptrana Dashboard page appears.
Apptrana is designed to address the shortcomings in existing cloud security solutions based on your existing risk posture as we Detect your risks continuously, Protect your application immediately, ensure round-the-clock availability, improve website performance instantly, 360 degrees view of your application security etc.
Dashboard or Sites Protected page appears as an entry point of Apptrana portal. No data is visible as the domain is just onboarded. An auto-scan will be in progress with successful configuration.
Once the DNS change is successful, an auto-scan will begin and it can be viewed in Detect page. If auto-scan is not started, click Auto-scan button in Detect Summary page.
We suggest you to perform Manual Pen Testing as our experts get right into detecting for any business logic vulnerabilities and other vulnerabilities with logical testing.
Go through our Apptrana Docs on each page of Apptrana portal as we get into each detail of features.